As AI agents take on actions once performed only by humans, traditional identity systems can’t provide clear delegation or accountability. StrongDM ID gives every agent a unique, verifiable identity linked to a human sponsor, ensuring organizations always know who authorized every action. In the next era of identity, authentication matters—but delegation defines trust.
Posts by Category:
- Security
- Access
- DevOps
- Privileged Access Management
- Auditing
- Zero Trust
- Compliance
- Policy
- Databases
- SOC 2
- Authentication
- Identity and Access Management
- Team
- Compare
- Engineering
- Integrations
- Product
- Kubernetes
- AWS
- Productivity
- Podcasts
- SSH
- Observability
- HIPAA
- ISO 27001
- Role-Based Access Control
- Dynamic Access Management
- Secure Access Service Edge
- Webinars
- Events
- NIST
- Onboarding
- Passwordless
- Offsites
- Platform
- PCI

As AI agents take on actions once performed only by humans, traditional identity systems can’t provide clear delegation or accountability. StrongDM ID gives every agent a unique, verifiable identity linked to a human sponsor, ensuring organizations always know who authorized every action. In the next era of identity, authentication matters—but delegation defines trust.
The modern cloud is fast, dynamic, and complex. But legacy security tools can’t keep up. As containers and ephemeral resources constantly change, and access requests surge, security teams are left scrambling. Entitlements pile up, visibility fades, and audits become a nightmare.

The modern cloud is fast, dynamic, and complex. But legacy security tools can’t keep up. As containers and ephemeral resources constantly change, and access requests surge, security teams are left scrambling. Entitlements pile up, visibility fades, and audits become a nightmare.

StrongDM debuts in Gartner’s Magic Quadrant for PAM, redefining privileged access with real-time, policy-based authorization for modern cloud environments.
StrongDM debuts in Gartner’s Magic Quadrant for PAM, redefining privileged access with real-time, policy-based authorization for modern cloud environments.
The modern cloud is fast, dynamic, and complex. But legacy security tools can’t keep up. As containers and ephemeral resources constantly change, and access requests surge, security teams are left scrambling. Entitlements pile up, visibility fades, and audits become a nightmare.
This guide is your merger and acquisition security checklist, a 7-day playbook for securing privileged access during M&A. It’s built on lessons from enterprise CISOs, industry best practices, and what we see every day at StrongDM.

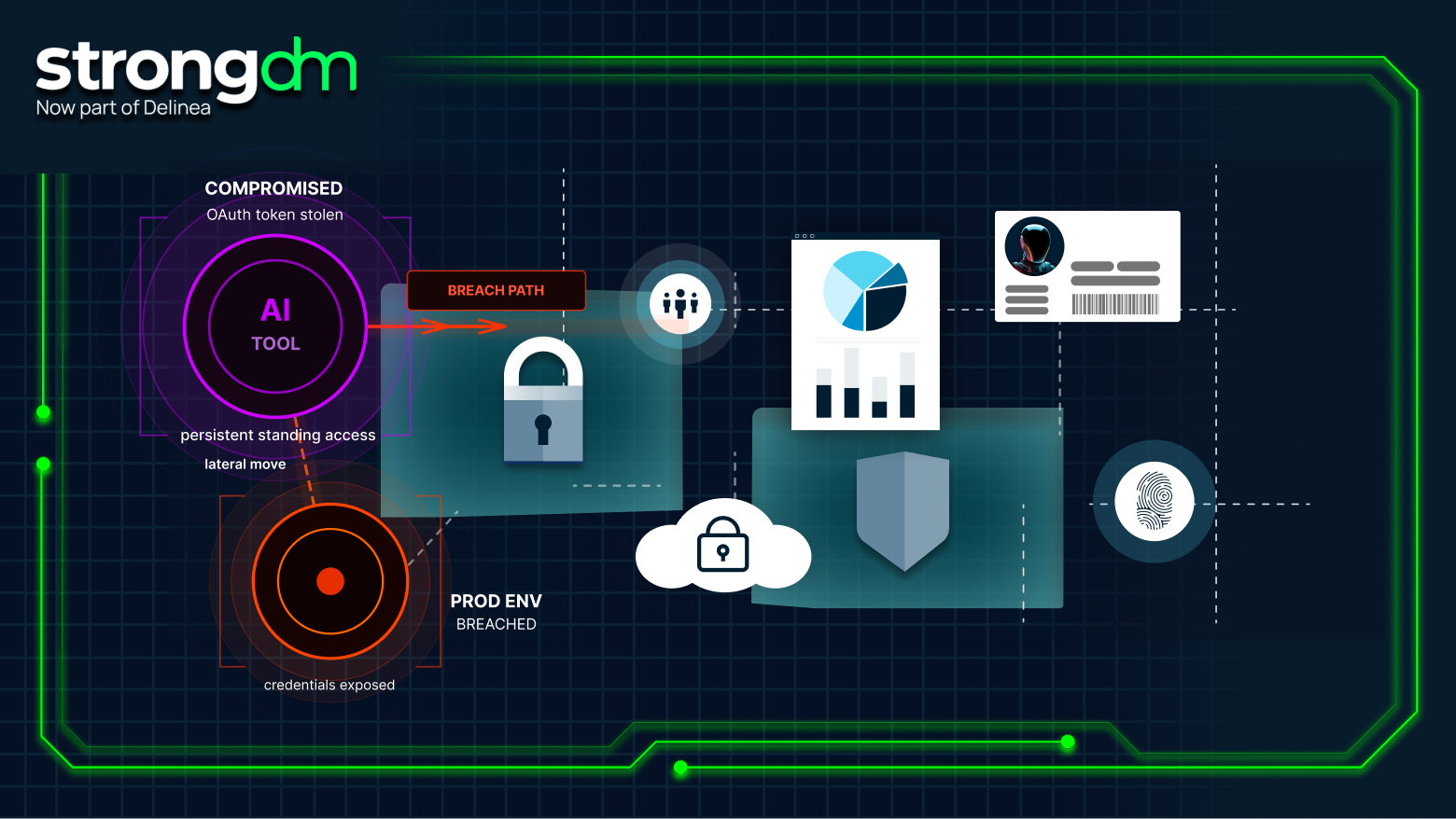
Non-human identities are fueling secrets sprawl, and vaults alone can’t stop it. Learn why NHIs are the primary source of leaked secrets, the limits of traditional secret stores, and how StrongDM governs access in real time without exposing credentials.

Access certification is more than a checkbox; it’s how you prove and enforce least privilege at scale. It ensures every user, system, and role has only the access they need, nothing more. In this guide, you’ll learn how to run access certifications that satisfy auditors, reduce insider threats, and clean up outdated privileges. You’ll explore common types (manual vs. automated, user-based vs. resource-based), challenges, and how modern teams streamline the process with real-time visibility and
Discover why traditional secrets management isn't enough. StrongDM Managed Secrets offers vault-agnostic, Zero Trust security with secretless access, dynamic policy enforcement, automated rotation, and unified audits—perfect for complex enterprise environments.

As teams grow and roles shift, it’s easy for permissions to get out of sync. That’s where user access reviews come in—they ensure every employee, vendor, or service account has exactly the access they need, and nothing more.Regular reviews reduce risk, prevent privilege creep, and help meet compliance requirements like SOX, ISO 27001, and HIPAA. But manual reviews? They’re slow, messy, and often incomplete.This guide breaks down the essentials of access reviews—what they are, why they matter,
Secrets management is the practice of securely storing, accessing, and controlling digital authentication credentials such as passwords, API keys, certificates, and tokens used by applications and systems. It ensures that sensitive information is protected from unauthorized access, while supporting automation, compliance, and security across modern infrastructure.
Let’s talk about the unsung heroes of your on-premises infrastructure: network devices. These are the routers, switches, and firewalls that everyone forgets about…and takes for granted—until something breaks. And when one of those somethings breaks, it leads to some pretty bad stuff. If your network goes down, that’s bad, bad, bad for business. But if those devices lack the necessary security, well, that can leave you exposed in an incredibly dangerous way.