As AI agents take on actions once performed only by humans, traditional identity systems can’t provide clear delegation or accountability. StrongDM ID gives every agent a unique, verifiable identity linked to a human sponsor, ensuring organizations always know who authorized every action. In the next era of identity, authentication matters—but delegation defines trust.
Posts by Category:
- Security
- Access
- DevOps
- Privileged Access Management
- Auditing
- Zero Trust
- Compliance
- Policy
- Databases
- SOC 2
- Authentication
- Identity and Access Management
- Team
- Compare
- Engineering
- Integrations
- Product
- Kubernetes
- AWS
- Productivity
- Podcasts
- SSH
- Observability
- HIPAA
- ISO 27001
- Role-Based Access Control
- Dynamic Access Management
- Secure Access Service Edge
- Webinars
- Events
- NIST
- Onboarding
- Passwordless
- Offsites
- Platform
- PCI

As AI agents take on actions once performed only by humans, traditional identity systems can’t provide clear delegation or accountability. StrongDM ID gives every agent a unique, verifiable identity linked to a human sponsor, ensuring organizations always know who authorized every action. In the next era of identity, authentication matters—but delegation defines trust.
The modern cloud is fast, dynamic, and complex. But legacy security tools can’t keep up. As containers and ephemeral resources constantly change, and access requests surge, security teams are left scrambling. Entitlements pile up, visibility fades, and audits become a nightmare.

The modern cloud is fast, dynamic, and complex. But legacy security tools can’t keep up. As containers and ephemeral resources constantly change, and access requests surge, security teams are left scrambling. Entitlements pile up, visibility fades, and audits become a nightmare.

StrongDM debuts in Gartner’s Magic Quadrant for PAM, redefining privileged access with real-time, policy-based authorization for modern cloud environments.
StrongDM introduces Leash, an open-source project delivering real-time policy enforcement for agentic AI. Gain visibility, control, and safety over autonomous workloads with unified access and runtime security.
StrongDM debuts in Gartner’s Magic Quadrant for PAM, redefining privileged access with real-time, policy-based authorization for modern cloud environments.
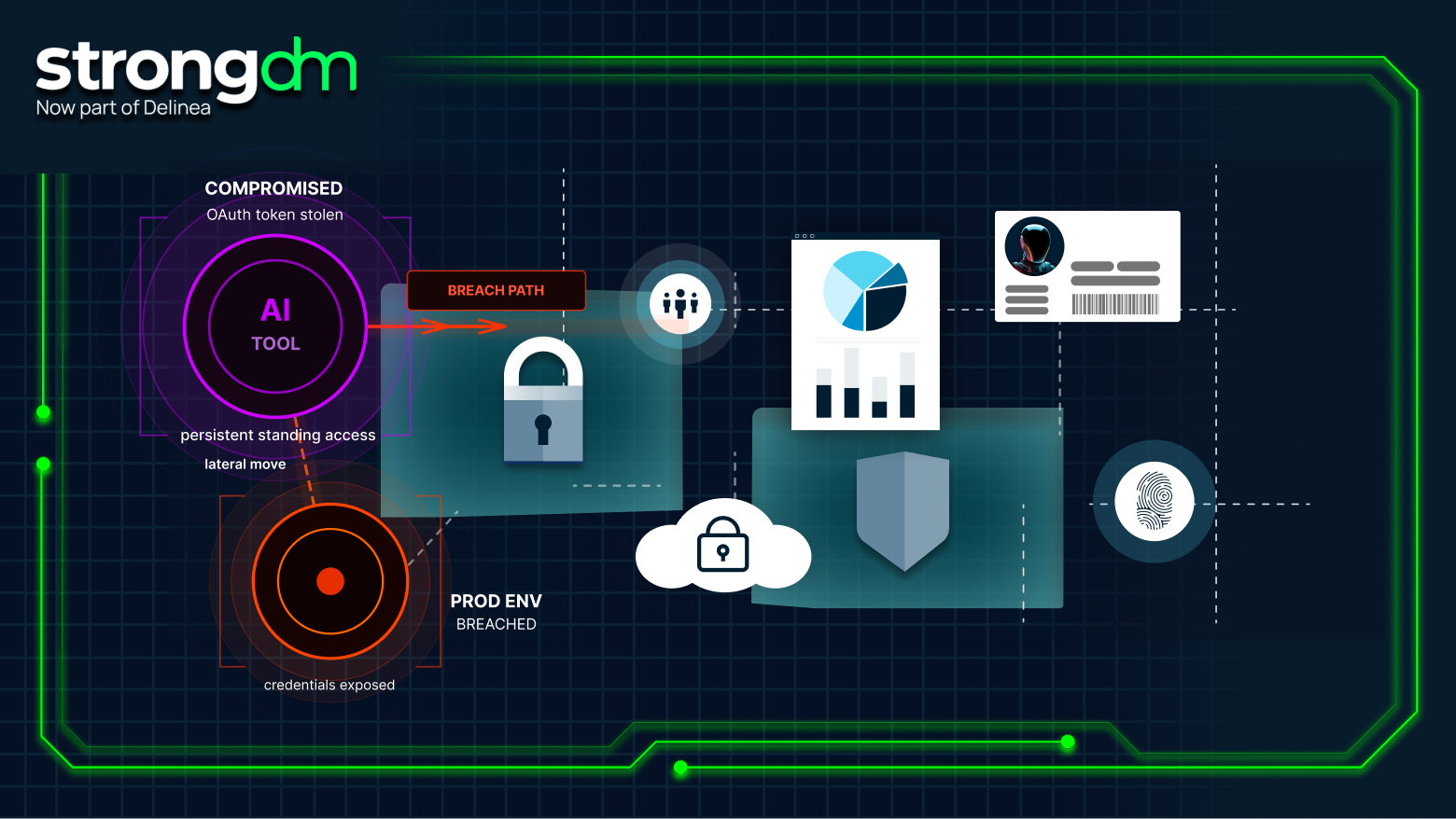
AI agents act autonomously, not just as tools. Learn why enterprises need runtime governance to secure, observe, and control AI behavior in real time.
The modern cloud is fast, dynamic, and complex. But legacy security tools can’t keep up. As containers and ephemeral resources constantly change, and access requests surge, security teams are left scrambling. Entitlements pile up, visibility fades, and audits become a nightmare.
The terms “multi-cloud” and “hybrid cloud” are often used interchangeably, but they solve very different problems. Multi-cloud uses multiple public cloud providers. A hybrid cloud blends public cloud with private or on-prem infrastructure. Your goals, compliance needs, and existing architecture determine which is right for you.
This guide covers the core risks of hybrid cloud security, compliance, and operational, and the eight best practices for locking them down, from Zero Trust and JIT access to unified monitoring, segmentation, and incident response.
This guide lays out a clear framework for evaluating database security tools, focusing on the risks they mitigate, the controls they deliver, and the outcomes they enable. From access and auditing to encryption, posture management, and recovery, we’ll highlight the best solutions and how they fit together
Segregated compute is more than a checkbox; it’s a core requirement in frameworks like PCI DSS, HIPAA, and FedRAMP. At its simplest, it means no user should ever connect directly to sensitive workloads. Every connection must be isolated, controlled, and auditable.