Kubernetes security is the practice of protecting containerized workloads and cluster components from unauthorized access, misconfigurations, and vulnerabilities. It involves securing the infrastructure, clusters, containers, and application code through layered controls like RBAC, network policies, image scanning, and runtime protection.
Posts by Category:
- Security
- Access
- DevOps
- Privileged Access Management
- Auditing
- Zero Trust
- Compliance
- Policy
- Databases
- SOC 2
- Authentication
- Identity and Access Management
- Team
- Compare
- Engineering
- Integrations
- Product
- Kubernetes
- AWS
- Productivity
- Podcasts
- SSH
- Observability
- HIPAA
- ISO 27001
- Role-Based Access Control
- Dynamic Access Management
- Secure Access Service Edge
- Webinars
- Events
- NIST
- Onboarding
- Passwordless
- Offsites
- Platform
- PCI
StrongDM’s Next-Gen Kubernetes provides secure, seamless access to Kubernetes clusters at scale. By eliminating standing privileges and enforcing Zero Trust security principles, StrongDM helps security teams maintain tight access controls without slowing down DevOps workflows.
Microservices make applications more scalable and resilient, and Kubernetes is the backbone that keeps them running smoothly. By orchestrating containers, handling service discovery, and automating scaling, Kubernetes simplifies microservices management—but it also introduces complexity. This guide covers key principles, deployment strategies, and security best practices to help you navigate microservices in Kubernetes. Plus, see a modern way of simplifying access and security, so your teams
Kubernetes observability is the practice of monitoring and analyzing a Kubernetes environment through metrics, logs, and traces to gain visibility into system performance and health. It enables teams to detect and resolve issues proactively, optimize resource utilization, and maintain cluster reliability through real-time insights and automated monitoring tools.

This article breaks down Kubernetes Ingress, explaining how it manages external access to services, routing configurations, and best practices. You’ll learn how Ingress differs from Load Balancers, how controllers enforce routing rules, and how to choose the right setup for your needs.
In this article, we explore everything you need to know about Kubernetes Secrets and how to manage sensitive information in your Kubernetes clusters. You'll learn how to create different types of secrets, understand the various creation methods using kubectl, and discover best practices for using secrets in your applications. By the end of this article, you'll have a comprehensive understanding of how to securely handle credentials, API keys, certificates, and other sensitive data within your

Kubernetes (K8S) has revolutionized software development, but managing such a complex system with numerous components can be challenging. Fortunately, there are several best practices your team can adopt to secure your K8S environment and reduce your attack surface. By implementing these Kubernetes ...
Kubernetes is a popular tool for managing synchronized groups, or clusters, of computers. Users employ it to configure and deploy applications in parallel across clusters on your networks. The kubectl command line tool in Kubernetes lets you send instructions to and receive information from your clusters. This kubectl cheat sheet is a quick guide to getting started with kubectl, including installation, configuration, key commands, and efficiency tips.

Kubernetes pod restarts are important for efficiently managing containerized applications in a dynamic microservices architecture. Understanding how to effectively restart pods using kubectl will help you streamline operations and minimize downtime. This article describes five methods to restart Kubernetes pods empowering you to maintain application health and performance confidently.
If you’re Kuberntes admin and you’re not familiar with the tactics outlined in the MITRE ATT&CK framework, this blog post is for you. MITRE ATT&CK framework is an extensive knowledge base of tactics and techniques employed by bad actors that defensive security experts use to help defend their organizations against attack, and many times, used by their offensive security counterparts to test their weaknesses.
The CIS Kubernetes Benchmark is a set of prescriptive recommendations assembled to guide administrators to achieve good security hygiene and results in strength security outcomes for their Kubernetes environments.
Secure access controls must be applied universally and consistently across all your infrastructure—from the Linux boxes in your datacenter to your Kubernetes clusters in AWS. StrongDM Dynamic Access Management is uniquely positioned to provide seamless, secure access across your entire stack, simplifying access management and compliance for your legacy systems and modern cloud stack.
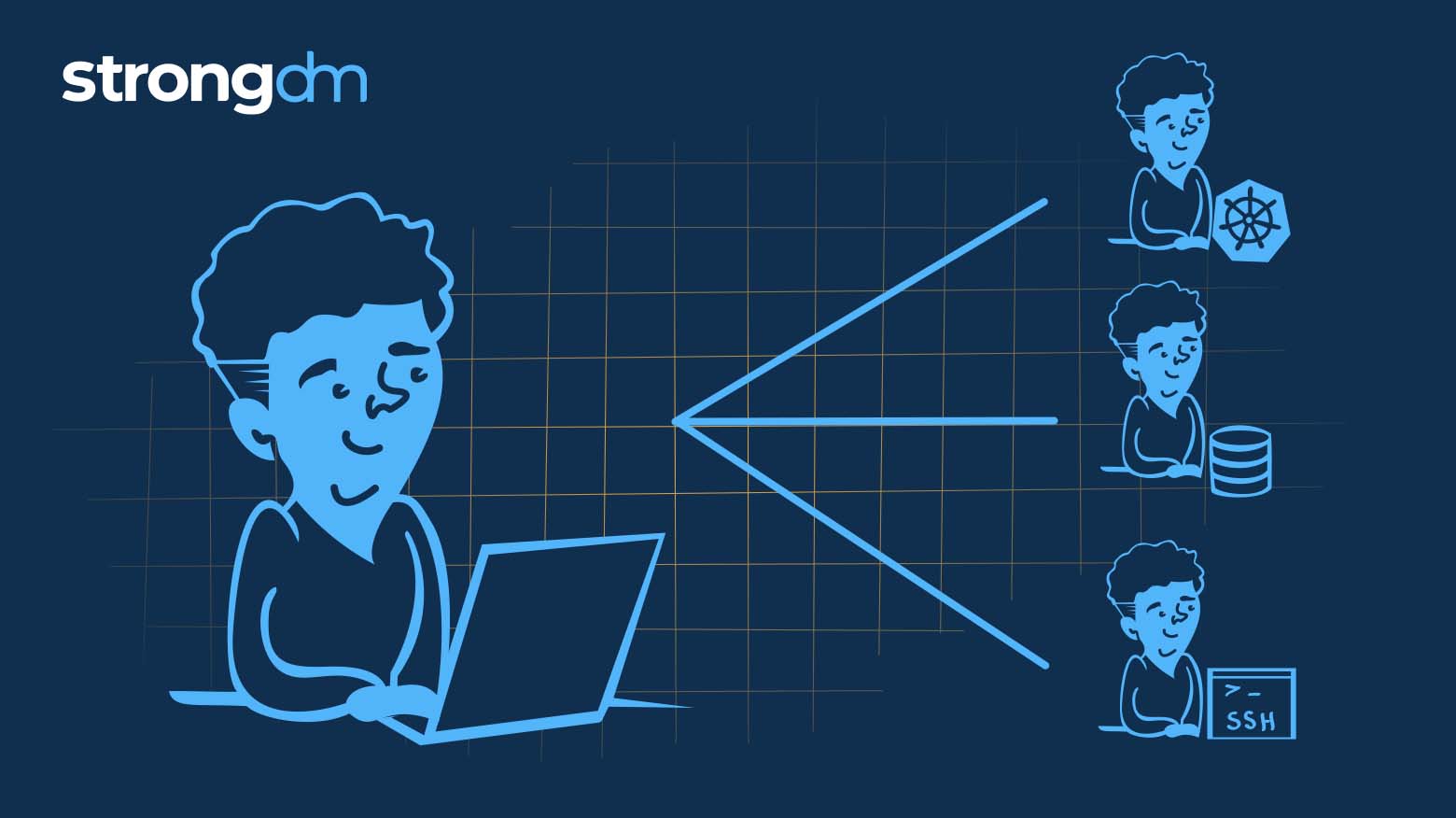
Learn how Remote Identities helps you leverage SSH and k8s capabilities to capitalize on infrastructure workflow investments you’ve already made.