Latest blog posts from John
User provisioning is the process of managing user access within an enterprise. It involves creating, managing, and deprovisioning user accounts and access rights across various systems and applications. This includes setting up accounts, assigning roles and permissions, and managing identities.
Audit logging is essential for maintaining a secure and compliant IT infrastructure. By capturing detailed records of system activities, audit logs provide insights into user actions, system events, and potential security threats. Understanding audit logging helps you identify and address vulnerabilities, ensure regulatory compliance, and enhance overall system integrity.
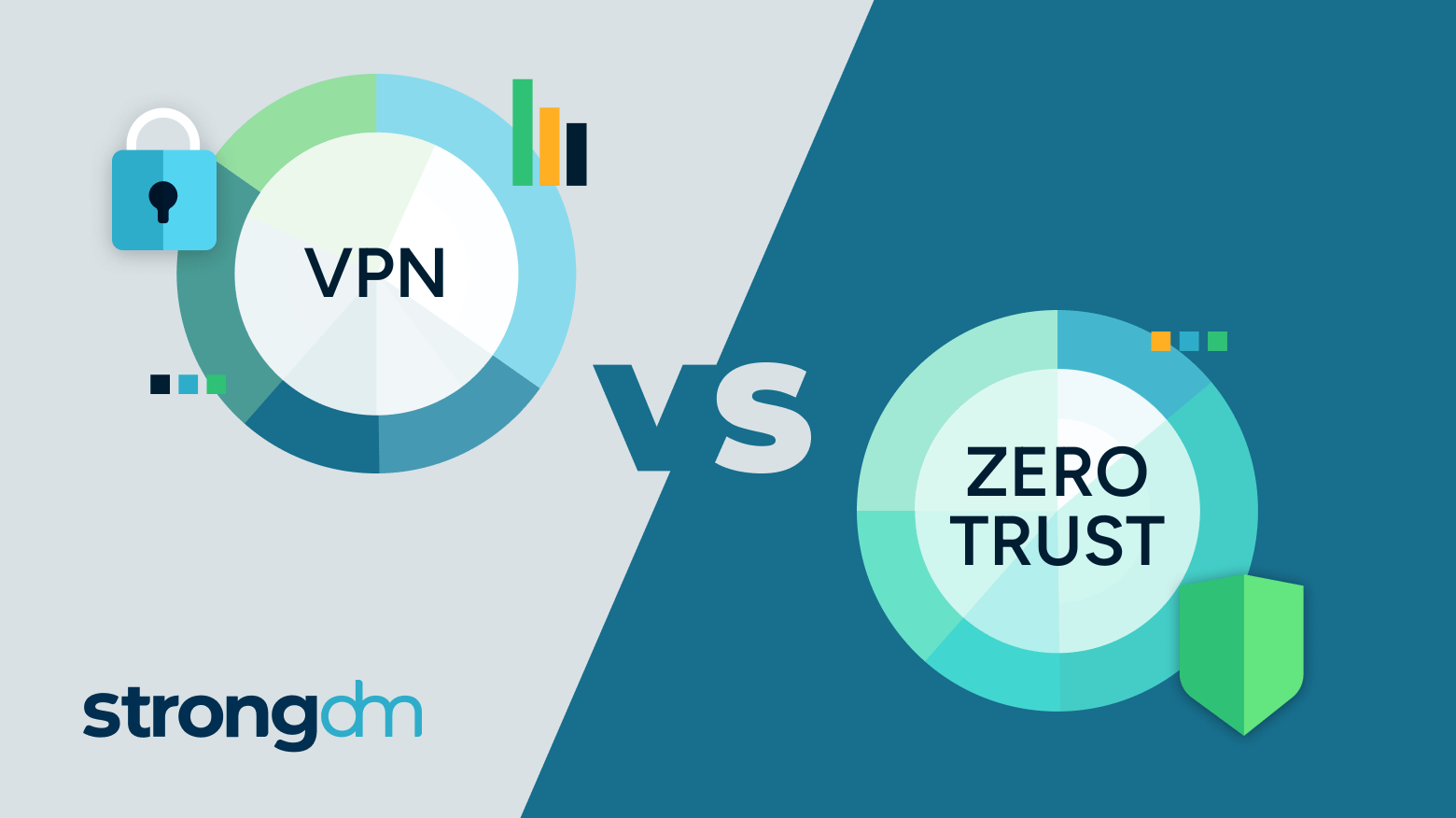
Understanding the core differences between a Zero Trust architecture and a Virtual Private Network (VPN) is an important step in shaping your organization’s cybersecurity strategy. Zero Trust and VPNs offer distinct approaches to security; knowing their functionalities and security philosophies helps you understand when to select one or the other to protect your data effectively—a strategic necessity for robust cybersecurity.

StrongDM is pleased to see that, in April 2024, the National Security Agency of the United States, has released a Cybersecurity Information (CSI) sheet that recommends why and how organizations, public and private, should adopt the Zero Trust (ZT) security model for their data tier of infrastructure. At the core of the recommendations, an organization needs to know what data it possesses, how that data is being accessed, and how to control access to that data.

User authentication plays an essential role in securing networks and ensuring that only authorized users can access sensitive data. As our infrastructure transitions from traditional on-premises setups to cloud and hybrid environments, our authentication methods must continue evolving.
A cybersecurity audit is a comprehensive assessment of your organization's information systems, networks, and processes that identify vulnerabilities and weaknesses that cybercriminals could exploit. The audit also evaluates the effectiveness of your security controls, policies, and procedures and determines if they align with industry best practices and compliance standards.
Zero trust is a security and authentication model that eliminates the assumption of trust and shifts the focus from a traditional security parameter, like a VPN or firewall, to the individual user. Nearly all (92 percent) cybersecurity professionals agree that it’s the best network security approach that exists. In this article, we’ll evaluate the top nine zero trust solutions and help you decide which is right for your organization.

Both AWS Systems Manager (SSM) Session Manager and StrongDM are solutions for gaining remote access to critical infrastructure. Yet, while they share some of the same capabilities required of an enterprise access management platform, the execution and the ultimate goals they accomplish for security and compliance teams are very different.

Unauthorized access—the unauthorized entry or use of an organization's systems, networks, or data by individuals without permission—is a common way for bad actors to exfiltrate data, inject malicious code, and take advantage of all types of breaches, and can have severe consequences for an enterprise and its customers.
Last week, Red Hat issued a warning regarding a potential presence of a malicious backdoor in the widely utilized data compression software library XZ, which may affect instances of Fedora Linux 40 and the Fedora Rawhide developer distribution. CISA, or Cybersecurity & Infrastructure Security Agency, confirmed and issued an alert for the same CVE.
Healthcare data security protects sensitive patient information and related data from unauthorized access, use, or disclosure. The effective implementation of healthcare data security requires implementing cybersecurity measures to ensure healthcare data confidentiality, integrity, and availability. It must also include compliance with relevant regulations such as the Health Insurance Portability and Accountability Act (HIPAA).

Creating Postgres users isn't just a routine step in the complicated world of database management; it's a critical strategy that has a significant impact on how PostgreSQL databases operate and remain secure. An increasing number of organizations depend on sophisticated data systems, so it's critical to recognize the value of Postgres users. This blog post walks you through the steps of creating a Postgres user, as well as, explores the significance of these users in database administration,

Cozy Bear specializes in targeting governments, diplomatic entities, non-governmental organizations (NGOs), and IT service providers, primarily in the U.S. and Europe. These state-sponsored groups aim to clandestinely gather strategic and sensitive information for Russia, maintaining prolonged access without raising suspicions.
The CSA CCM is a cybersecurity control framework specifically designed for cloud computing. It outlines a comprehensive set of best practices and security controls across 17 domains that are designed to ensure that cloud environments are secure and resilient against an ever expanding threat landscape. The CCM framework is structured to provide clarity and actionable guidance for the implementation of security measures in a prescriptive and adaptable way for recognized compliance standards and

