Simplifying AWS Access with StrongDM Without Compromising Security Posture

Since Amazon Web Services first announced it in 2011, AWS IAM has evolved to become the gateway to the AWS Cloud. Organizations cannot interact with their cloud resources and its many services without it. Identity, not networking, is the real access boundary.
This evolution comes at a price, however: complexity.
Today, organizations can and should federate identities and centrally manage access to their applications via an identity provider. Then, there’s the best practice for “breaking glass” scenarios when emergency access is needed, but the end-user experience falls short.
Obtaining access to the AWS Management Console and AWS CLI should not be a crazy multi-step process for users with so many choices of AWS accounts in multi-account environments that an engineer has a hard time figuring out which one she actually needs to access. From a provisioning perspective, this practice ensures the granting of too much access for convenience, thereby creating a broad attack surface nightmare for security teams.
Thankfully, there’s a better way with StrongDM.
We’ll share a story about how developers could more easily access their AWS resources. Cloud administrators also get the advantage that the keys to their AWS empire are protected and never shared.
Let’s say a newly hired developer, Emily, was told to request access to 3 AWS accounts hosting development environments and CI/CD automation tools.
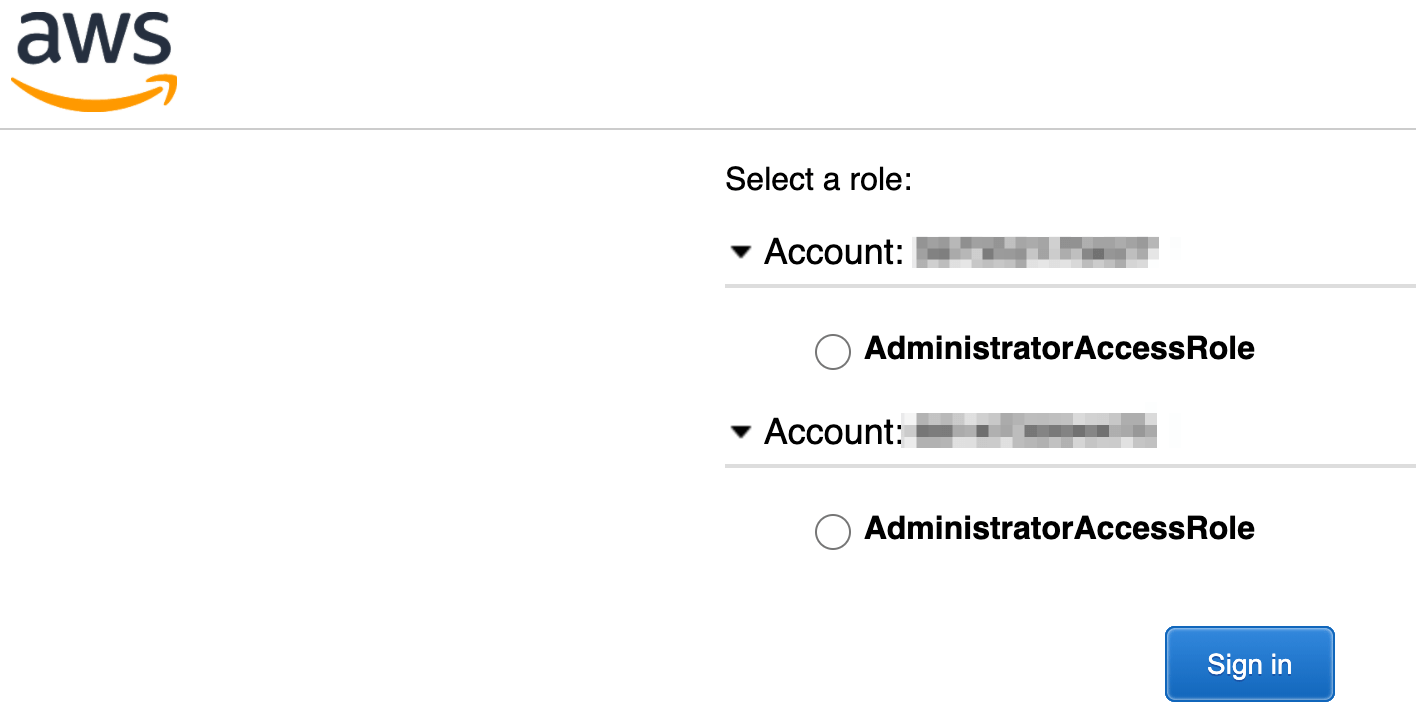
Emily’s company uses StrongDM to manage access to company resources dynamically. So all she needs to do is log in to the StrongDM app and find that her AWS accounts are listed for both AWS Console and AWS CLI, and she’s a happy, productive camper!
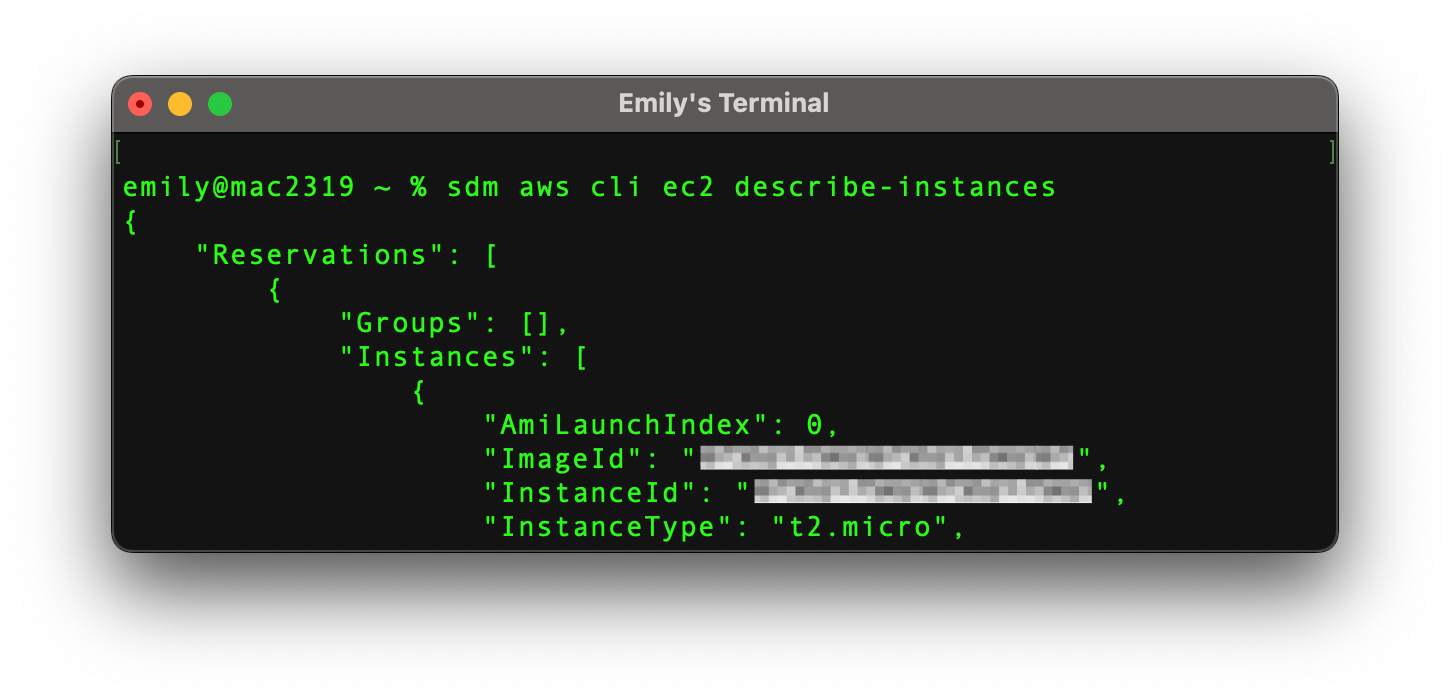
She can log in directly to the AWS Console from the StrongDM app. For CLI access, she only needs to execute the sdm CLI command in a terminal session. No static AWS credentials or role assumption is needed. All she had to do was to set the default AWS region, StrongDM took care of the rest!
But oh no! Just three days into her new job, a production incident on an RDS MySQL database in a production AWS account gets thrown in her lap, and she’s the expert to fix it. But developers don’t have access to Prod. Now what?
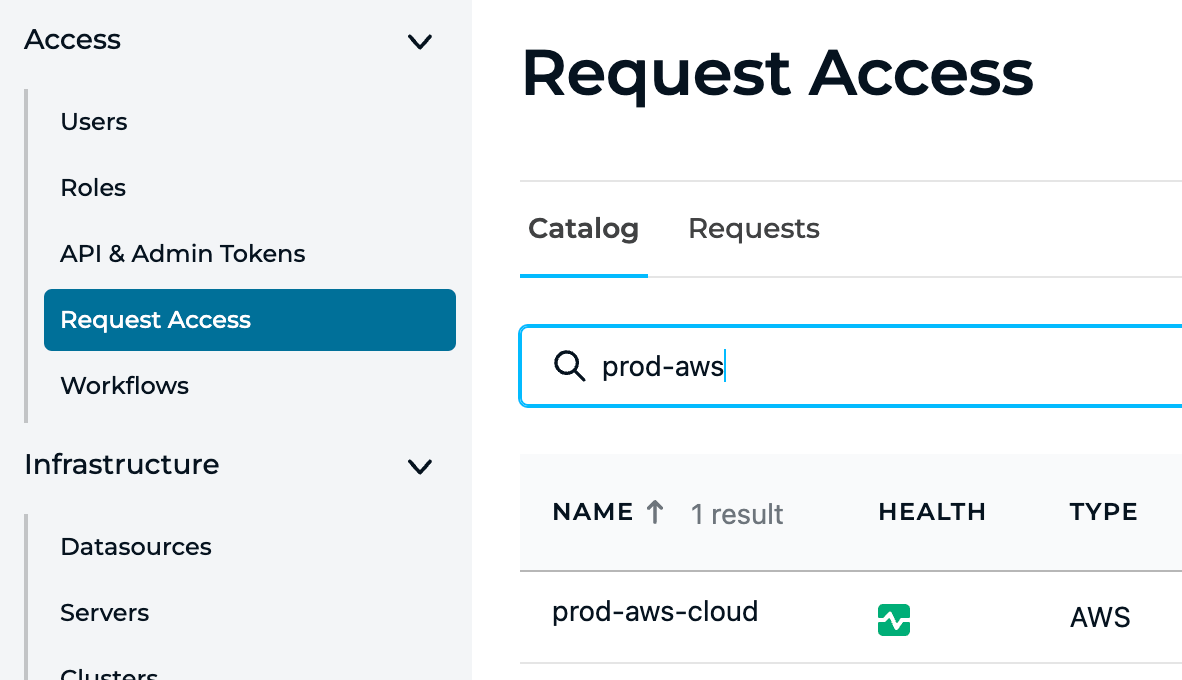
There’s a super simple way for Emily to gain temporary access to the Prod AWS account and the RDS instance via StrongDM’s Access Workflows! From the StrongDM app, she opens the StrongDM web app and requests access to AWS Prod for the next 2 hours, which is how long she estimates it will take her to do her magic on the database. Her request for access is automatically approved by the access workflow because StrongDM was configured to allow Emily to work on the dynamic set of cloud resources for the app she's responsible for, and the amount of time the access was requested was within the workflow’s pre-approved parameters. (She’s also super stoked because she will soon be able to do this all via Slack!)
Emily sees the new AWS Prod resources in her StrongDM desktop app and can now save the day on the incident. After a little less than 2 hours, the incident is closed, and Emily’s access to Prod is automatically revoked.
Emily isn’t the only hero here, however. Her Identity and Security team, whom she’s never met, chose to use StrongDM. This scenario is as much, if not more so, of a win for her company’s security and compliance posture as it is for the simplicity of Emily’s experience.
- Emily’s company is somewhere between the Advanced and Optimal stages of the CISA Zero Trust Maturity Model - where most processes are automated and Just-in-Time, Just-Enough, Dynamic Access implemented
- Many regulatory and industry compliance controls are met, including full audit logging and session recording.
- The security team is also well on the way to achieving Zero Standing Privileges - where no baseline access is granted to identity profiles.
- The security team has the power of StrongDM’s Dynamic Access capabilities: Access Workflows; Dynamic Access Rules (tags FTW!); and Temporary, Self-expiring access duration.
The Alternative Nightmare
In Emily’s previous job, where StrongDM wasn’t used, all of this would have followed the painful processes developers have grown accustomed to: long delays to obtain access, too much reliance on tribal knowledge, and manual configuration of the tools she needs to use for her job.
And for the security team, Emily would have had too much privilege, lingering access that was no longer needed, or static credentials that may or may not have been stored in a secure way. In short: too much access for too long.
It’s almost a guarantee that Emily’s first production incident would have been much longer than 2 hours, and much of that time would have been waiting for access to be provisioned. Even longer if the incident was in the middle of the night.
John’s Personal Note
I’ve been an AWS practitioner and user for a long time, managing DevOps, Platform Engineering, and Development teams, and as soon as I experienced how easy and secure it was to get access to the AWS accounts I need to get my job done with StrongDM, I had to shout it to the world! I’m new to StrongDM, but not to Cloud Security.
If you’re a cloud or security professional and have questions, comments or ideas, please reach out to me … I would love to hear from you! Even better, sign up for a free trial so you can see for yourself, then reach out to me! If you’re attending AWS re:Invent in the fall, please swing by our booth and we can have a conversation then.
Next Steps
StrongDM unifies access management across databases, servers, clusters, and more—for IT, security, and DevOps teams.
- Learn how StrongDM works
- Book a personalized demo
- Watch a StrongDM walkthrough


About the Author
John Martinez, Technical Evangelist, has had a long 30+ year career in systems engineering and architecture, but has spent the last 13+ years working on the Cloud, and specifically, Cloud Security. He's currently the Technical Evangelist at StrongDM, taking the message of Zero Trust Privileged Access Management (PAM) to the world. As a practitioner, he architected and created cloud automation, DevOps, and security and compliance solutions at Netflix and Adobe. He worked closely with customers at Evident.io, where he was telling the world about how cloud security should be done at conferences, meetups and customer sessions. Before coming to StrongDM, he lead an innovations and solutions team at Palo Alto Networks, working across many of the company's security products.
You May Also Like




