
Latest blog posts from John

Identity and access management (IAM) is a collection of technologies, policies, and procedures designed to guarantee that only authorized individuals or machines can access the appropriate assets at the appropriate times. While it is an effective approach to enterprise security, IAM implementations are complex undertakings. If not done correctly, it can create security gaps that leave your organization at increased risk of a breach. Taking a measured approach will ensure your deployment is

re:Invent 2023 was AWS’ 12th conference, and it did not disappoint. More than 50,000 of us descended onto Las Vegas for a week of learning, networking, and discussing all things cloud. The campus was insanely large, spanning most of the Las Vegas strip, so that meant we got our steps in! We had some fun along the way, as well, at the many social gatherings, parties and amazing musical experience re:Play.
The AWS Well-Architected Framework has been a staple for many years for AWS practitioners of all sorts, including cloud architects and platform engineers. It’s a blueprint for architectural and design best practices that will lay the foundation for resilience, operational efficiency, and security on the AWS Cloud.
If you’re Kuberntes admin and you’re not familiar with the tactics outlined in the MITRE ATT&CK framework, this blog post is for you. MITRE ATT&CK framework is an extensive knowledge base of tactics and techniques employed by bad actors that defensive security experts use to help defend their organizations against attack, and many times, used by their offensive security counterparts to test their weaknesses.
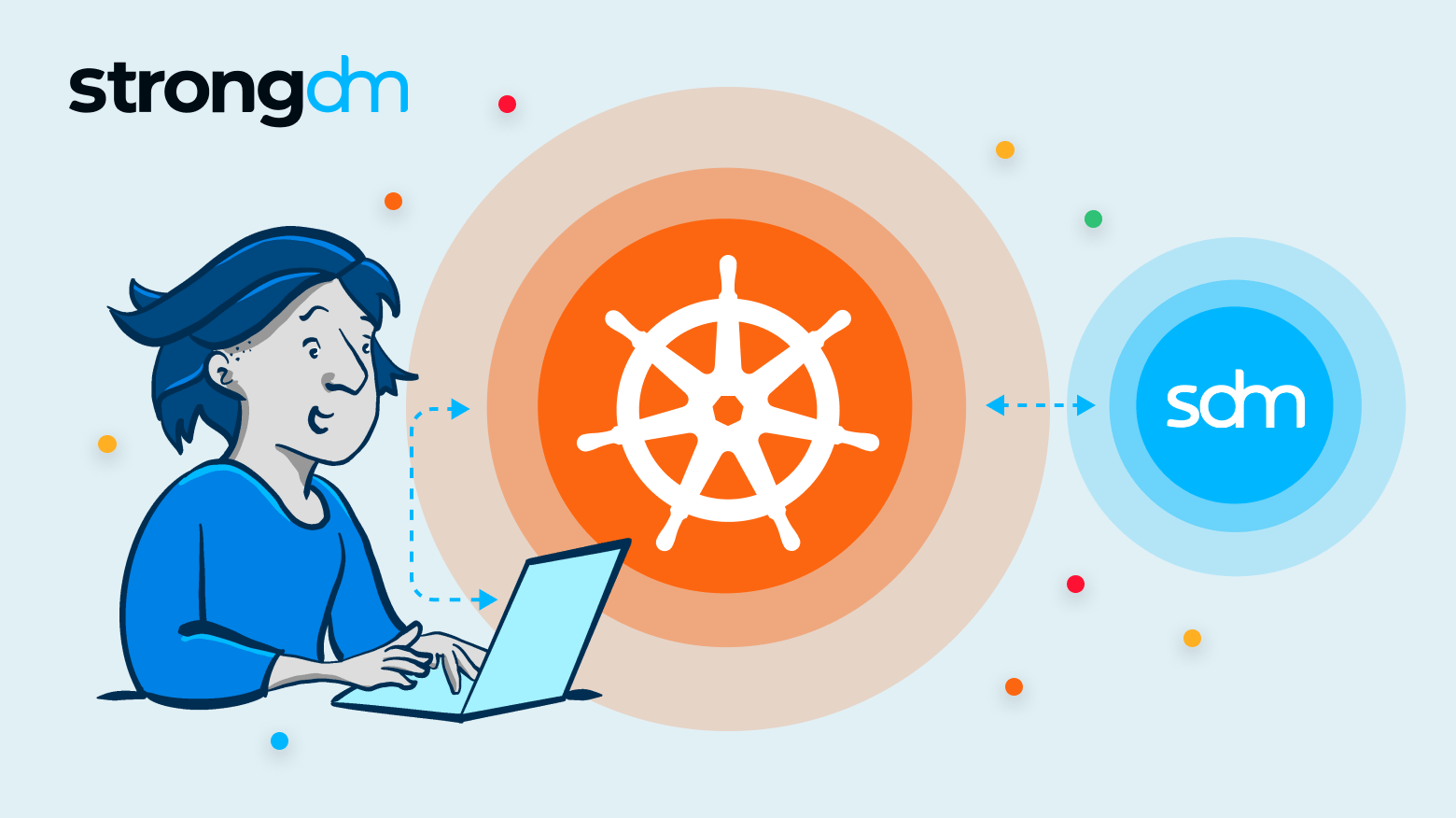
The CIS Kubernetes Benchmark is a set of prescriptive recommendations assembled to guide administrators to achieve good security hygiene and results in strength security outcomes for their Kubernetes environments.

Since Amazon Web Services first announced it in 2011, AWS IAM has evolved to become the gateway to the AWS Cloud. Organizations cannot interact with their cloud resources and its many services without it. Identity, not networking, is the real access boundary.
AWS Secrets Manager is a popular and highly intuitive secrets management tool that lets organizations automate secrets rotation processes and securely store, manage, and audit IT credentials. However, certain AWS Secrets Manager alternatives are available if you are looking to avoid getting tied down exclusively to AWS products or prioritize efficient user onboarding. In this product comparison guide, we evaluate AWS Secrets Manager competitors that can fill in some of its product gaps.
Microsoft Azure Key Vault is a cryptographic and secrets management solution for storing encryption keys, certificates, and passwords. While known for its interface simplicity and robust security, users should look to Azure Key Vault alternatives if they prioritize employee onboarding automation or need quick and easy implementation. This article evaluates Azure Key Vault competitors regarding security features, pricing, and usability to identify the best alternative options.
Google Cloud Secret Manager is an intuitive platform for managing API keys, user passwords, digital certificates, and other sensitive data and administering access control policies for business resources. While cost-friendly and reliable for securing Google Cloud applications, you should look to other Google Cloud Secret Manager competitors if you manage complex infrastructure and need multiple integrations.
Concerned about providing secure access to the data and tools employees need to do their jobs in a cloud or hybrid environment? Don’t worry. Solid strategies exist for protecting distributed resources. Zero Trust and SASE are two architectural approaches that provide strong security in today’s cloud-first world. The information in this article will help you decide which strategy works best for your business. Robust cloud security is attainable.
Secured authentication to databases and applications is crucial to enterprise cybersecurity management. Unfortunately, 82% of all breaches involve human error, including misused or compromised credentials that give threat actors unauthorized access to network resources. Luckily, there’s a solution that ensures security without the risks that come with traditional, credential-based authentication. This article discusses token-based authentication and explains why it's a reliable and flexible

Is your organization overwhelmed by rampant service account sprawl? Rest assured, you can regain control. Modern Privileged Account Management (PAM) tools and practices empower you to overcome the challenges of unchecked service accounts. The information in this article will help you understand the meaning of service accounts, so you can manage your organization’s service accounts more effectively and mitigate their risks. Robust security is attainable for all your privileged accounts.
Cloud native security solutions can help organizations like yours protect your cloud resources, no matter when you transitioned to the cloud. Here’s everything you need to know about integrating cloud native security.

In this article, we will spotlight 11 log management best practices you should know to build efficient logging and monitoring programs. You’ll learn how to establish policies and take a proactive approach to collecting, analyzing, and storing business-critical log data. By the end of this article, you’ll have a clearer understanding of how logs can help security teams detect suspicious activity, address system performance issues, identify trends and opportunities, improve regulatory compliance,

