What is Zero Standing Privilege (ZSP)? (And How They Work)


Written by
John MartinezLast updated on:
February 20, 2026Reading time:
Summary: Securing sensitive company data starts with limiting who can access that data, and adopting a zero standing privileges security approach is a great way to control access. In this article, we’ll discuss what zero standing privileges (ZSP) are, how standing privileges are created, and how just-in-time access makes a ZSP model feasible. We’ll explore the risks that accompany standing privileges, the benefits of a zero standing privilege philosophy, and best practices to follow when adopting a ZSP model. By the end of this article, you’ll be ready to incorporate a zero standing privilege philosophy into your security strategy.
What is Zero Standing Privilege (ZSP)?
Zero standing privileges (ZSP) is a privileged access management (PAM) strategy where organizations limit access to sensitive data by removing all permanent user access permissions.
ZSP supports zero trust security architecture by developing policies and controls that require users to always verify their identity before gaining access to the company’s IT infrastructure. These policies ensure that users receive access to systems, applications, servers, or other resources “just in time” to complete their daily work.
Just-in-time access (JIT) develops new credentials every time a user requests access to a resource. Then, those credentials are automatically destroyed once the user completes their task. Through this permissions strategy, organizations reduce their attack surface and limit how much data malicious actors can access if they capture an administrator’s credentials.
💡Make it easy: Just-in-Time Access works best when it is easy for the end user to request and receive access. It should also be auditing to map the end to end chain of events, who is requesting access, why they are requesting it, and for how long. Play the video below to see how easy StrongDM makes Just-in-Time access and try it for yourself.
Zero Standing Privilege vs. Least Privilege Model
We define privileges as the access permissions each user has to different components of a company’s IT infrastructure. The principle of least privilege focuses on allowing the most minimal access users need to perform their day-to-day tasks. The least permissions model is a fundamental component of a zero trust methodology. However, least privileged access still implies that some level of access is still standard for individual users.
Contrarily, zero standing privilege doesn’t assign any baseline access to user identity profiles. Instead, ZSP requires users to request access to any resource, so users can’t use their credentials to sign into any resource without express permission. Eliminating all standing privileges takes cybersecurity a step further by not only verifying the user for every login, but also verifying why the user needs access to the resource to reduce privilege abuse.
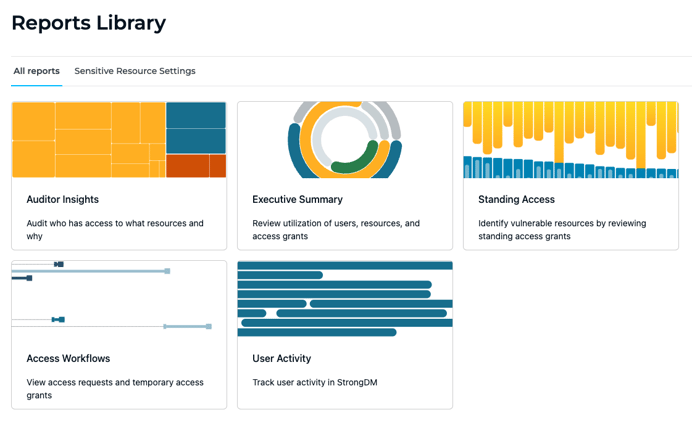
💡Make it easy: Fine-tune least privilege by analyzing and responding to comprehensive access insights. Easily report on which privileges are being used (or not). Try it yourself.
Standing Privileges: What Are They and How Are They Created?
Most traditional PAM tools operate by assigning “always-on” privileges for each system to individual users. Many tools also leverage role-based permissions to define which users have permanent access to certain systems. What these tools have in common is that users have constant access—or standing privileges—to resources based on factors like job level or department, not whether that user actually needs access to that resource.
Companies must create dedicated accounts for users and define criteria to help PAM tools determine which resources the user should have ready access to. These accounts often house the user credentials or secrets that allow them ongoing access to these resources. Naturally, these privileges are more expansive for system administrators.
Standing privileges allow users to access resources from anywhere at any time without authorization. Depending on the other security strategies in place, standing privileges may not even require a user to authenticate their identity before authorizing access to a system. While this may be convenient for users, standing privileges pose a substantial risk if malicious actors gain access to user credentials.
Risks of Standing Privileges
Providing permanent access to resources—especially with the rise of remote work—presents a lot of security issues for organizations. As IT environments continue to expand, companies with standing privileges need to constantly define who has access to which resources. This involves ongoing monitoring and management—especially when provisioning and deprovisioning access for new or departing employees—which can be a significant resource drain on an organization.
Even when companies use PAM solutions and vaults to manage passwords, they still pose a risk should those credentials fall into the wrong hands. With standing privileges, anyone who gains those credentials can breach any resource that the user has access to by moving laterally through the network. This is particularly threatening if a bad actor gains access to admin credentials, since an administrator may have extensive permissions for multiple systems or the ability to freely escalate privileges.
Since the impact of a breach can be much greater in an organization with standing permissions, even least privileged access risks are enough to dissuade cyber insurance companies from covering an organization. Traditional PAM solutions don’t offer strong enough security controls to prevent a breach from compromised credentials, so companies need to reimagine how they give users access to the resources they need.
Benefits of Zero Standing Privileges
Zero standing privileges may seem inconvenient for organizations accustomed to traditional PAM solutions. However, since standing privileges require so much work to securely maintain, a just-in-time, least privilege approach may ultimately be less expensive and time-consuming to manage once implemented.
ZSP leverages granular, policy-based security controls to grant users ephemeral access to the resources they need when they need them. The user’s access is automatically removed once they’ve completed their task and the access time limit expires, reducing the time IT teams spend provisioning and deprovisioning access. Limited access can also help an organization qualify for cyber insurance, which reduces the cost an organization must pay in the event of a breach.
One notable benefit of ZSP is the ability to limit excessive administrative user access. Admins often have high privilege levels and maintain too much control within an IT environment, presenting an exploitation risk. The zero standing privilege model prevents users from maintaining access they don’t need and reduces the passwords, secrets, and keys a company must maintain to remain secure.
Zero Standing Privileges and Just-in-Time (JIT) Access
Just-in-time access makes it possible to implement zero standing privilege. JIT access involves short-term or single-use access to resources by creating ephemeral credentials that expire once the user no longer needs access.
In a JIT workflow, users can easily request access to resources as needed and receive near-instant approval based on role-based or attribute-based access controls. These access controls can be applied to both human and non-human users for better access control.
Sometimes, a request for a new resource or elevated permissions may call for an administrator’s approval. A JIT workflow that’s integrated with a support platform can allow users to explain their need for elevated permissions and have their request approved or denied in moments. Plus, since all requests go through the JIT workflow, organizations can maintain logs and session records for easier auditing, too.
Zero Standing Privileges Best Practices
Building a workflow to support providing just-in-time access is essential to adopt ZSP. Maintaining a robust, modern workflow with your IT support team ensures that users get access when they need it and that there is a comprehensive log of each time users request permissions. Those logs make auditing and compliance reporting substantially faster and easier.
In these workflows, admins don’t need to personally grant or deny every request. Designing granular attribute-based or role-based access controls streamlines access provisioning by instantly granting a user’s request if they meet the required policy criteria. Admins should focus on strengthening these access controls regularly to reduce manual provisioning and fine-tune who needs access to which resources.
With strong access controls, organizations can eliminate static credentials for individual users and replace them with standing shared accounts. Companies can rotate credentials for these accounts and manage them in a vault to limit the risk of exposed user credentials.
How StrongDM Simplifies Zero Standing Privileges Implementation
StrongDM is a modern PAM solution that helps companies give their users secure, streamlined access to the resources they need. Our comprehensive Zero Trust Privileged Access Management (PAM) platform gives teams like yours complete control over who accesses which resources across your entire IT infrastructure—all from one easy-to-use dashboard.
Traditional PAM solutions make achieving zero standing privileges nearly impossible. With StrongDM, organizations can implement zero standing privileges and use just-in-time access to always verify users, ensuring the right users always have the right access at the right times. Slick admin controls help streamline approvals, while on-demand, approval-based access keeps your company agile.
Plus, granular logging and session recording turns cumbersome compliance reporting and monitoring into a piece of cake. StrongDM connects to every element in your tech stack, so you can track, audit and report on every query and action in any directory, application, server, and more. The Infrastructure Access Platform even seamlessly integrates with your chosen SSO and MFA tools, so you can strengthen your access controls without starting all over with new solutions.
Make Zero Standing Privileges a Reality with StrongDM
Creating a full zero trust architecture can be difficult, but managing strict user permissions doesn’t have to be.
StrongDM provides the most comprehensive Zero Trust PAM solution, making it simple for your team to give users access only when they need it keeping your organization's resources secure without slowing productivity. With StrongDM, your organization can easily eliminate thousands of credentials with zero standing privileges and just-in-time access, reducing the risk of a breach and keeping your data secure.
Try StrongDM free for 14 days today and see just how easy implementing zero standing privileges can be.
Next Steps
StrongDM unifies access management across databases, servers, clusters, and more—for IT, security, and DevOps teams.
- Learn how StrongDM works
- Book a personalized demo
- Watch a StrongDM walkthrough

Categories:

About the Author
John Martinez, Technical Evangelist, has had a long 30+ year career in systems engineering and architecture, but has spent the last 13+ years working on the Cloud, and specifically, Cloud Security. He's currently the Technical Evangelist at StrongDM, taking the message of Zero Trust Privileged Access Management (PAM) to the world. As a practitioner, he architected and created cloud automation, DevOps, and security and compliance solutions at Netflix and Adobe. He worked closely with customers at Evident.io, where he was telling the world about how cloud security should be done at conferences, meetups and customer sessions. Before coming to StrongDM, he lead an innovations and solutions team at Palo Alto Networks, working across many of the company's security products.
You May Also Like