Latest blog posts from Andrew

It is no surprise that President Joe Biden issued a Zero Trust executive order to protect federal government networks. On May 12, 2021, recognizing the dire situation, Executive Order (EO) 14028 was issued, focusing on protecting the U.S. from cybercriminals and cyberattacks. EO 14028 specifically recommends Zero Trust Architecture as necessary to defend the nation against threat actors. This post provides a summary of Executive Order 14028.
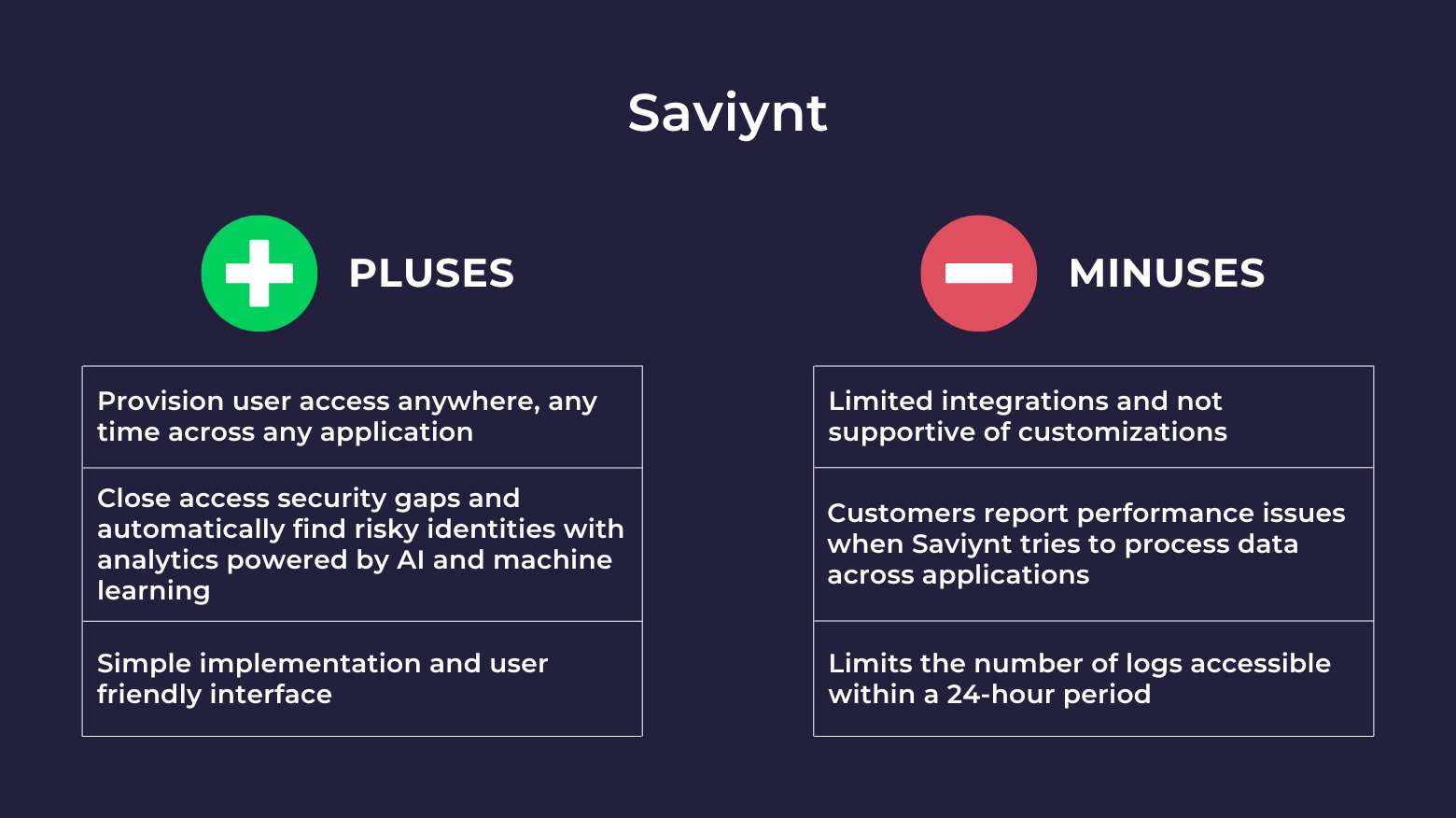
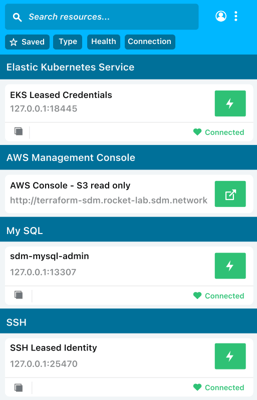
Saviynt is a popular identity and access management solution (IAM), but it may not be the best choice for every organization. In this article, we’ll explore powerful alternatives to Saviynt for companies with cloud-first IT infrastructure. By the end of this article, you’ll know whether Saviynt or one of these Saviynt competitors is the right fit for you.

In this article, we’ll explain the concept of automated provisioning and how it's used in identity and access management. You'll learn about the importance of automated provisioning in an organization's IT management and its benefits to businesses and system administrators. By the end of this article, you'll have a deep understanding of automated provisioning and how it works.

Enterprise cloud security is quickly becoming a cybersecurity best practice for large organizations. In this article, we’ll explore what enterprise cloud security is, why it’s important, and the challenges organizations experience with enterprise cloud adoption. You’ll learn about common cloud security issues and the best practices you should adopt to avoid those issues. By the end of this article, you’ll feel confident choosing the right enterprise cloud solution for your organization

To become ISO 27001 certified, organizations must align their security standards to 11 clauses covered in the ISO 27001 requirements. In this article, you’ll discover what each clause in part one of ISO 27001 covers. We’ll also take a big picture look at how part two of ISO 27001—also known as Annex A—can help your organization meet the ISO/IEC 27001 requirements.
In this article, we’ll review the leading privileged access management (PAM) solutions on the market. We’ll explore the pros and cons of the top privileged access management vendors so you can easily compare the best PAM solutions. By the end of this article, you’ll feel confident choosing the right privileged access management solution for your organization.
Following a HIPAA compliance checklist can help HIPAA-covered entities comply with the regulations and become HIPAA compliant. In this HIPAA compliance guide, we’ll review the 8 primary steps to achieving HIPAA compliance, tips on how to implement them, and frequently asked questions.
This article compares two Privileged Access Management (PAM) solutions, BeyondTrust vs. Thycotic (Delinea). It takes a closer look at how these PAM products work and how they fit in with your organization’s access management strategy. We’ll examine product summaries, use cases, and pros and cons. By the time you’re done reading this article, you’ll have a clear understanding of the similarities and differences between these PAM tools and be able to choose the tool that best fits your

This article looks at identity and access management (IAM) in cloud computing. You’ll learn how cloud IAM differs from traditional on-premises IAM, explore the benefits and challenges of cloud IAM, and discover how to choose the best cloud IAM system for your organization. By the end of the article, you’ll have a deeper understanding of the components of cloud IAM and how these software solutions can help mitigate cyberattacks that threaten your organization.

In this article, we'll cover the Authentication, Authorization, and Accounting (AAA) framework for cybersecurity, the meaning of each AAA component, and the benefits of using it for granular access control. You'll learn about different AAA protocols and how they relate to Identity and Access Management (IAM). By the end of this article, you'll fully understand AAA networking and how the model assists with network security and monitoring.

In this article, we’ll explore what data exfiltration is, the difference between exfiltration of data and data leakage, and how to detect data exfiltration. You’ll learn the dangers of data exfiltration in cybersecurity, data exfiltration examples, and the types of exfiltrated data that malicious actors target most. By the end of this article, you’ll know what causes data exfiltration, common data exfiltration tactics, and how to prevent data exfiltration in your organization.

This article examines what happens after companies achieve IT security ISO 27001 certification. We’ll answer questions about how to maintain ISO certification, how long ISO 27001 certification is valid, and the costs and risks of failing to maintain compliance. By the end of this article, you’ll know the certifying body requirements and what your checklist should look like for staying on top of your ISO 27001 certification.
This article compares two Privileged Access Management (PAM) solutions, CyberArk vs. BeyondTrust. It takes a closer look at what these two PAM products are, how they work, and what may make them fit well with your organization. We’ll explore product summaries, use cases, pros and cons, PAM features, and pricing. By the time you’re done reading this article, you’ll have a clear understanding of how these PAM tools operate and be able to choose the one that will work best for you.
In this article, you’ll what a honeypot is what honeypots are used for, and the benefits and risks associated with them. You’ll also learn about the different types and examples of honeypots and how they work. By the end of the article, you’ll have a deeper understanding of honeypots in cyber security, and how a secure infrastructure access platform can help you safeguard your network, systems, and apps without using a honeypot.