Latest blog posts from John
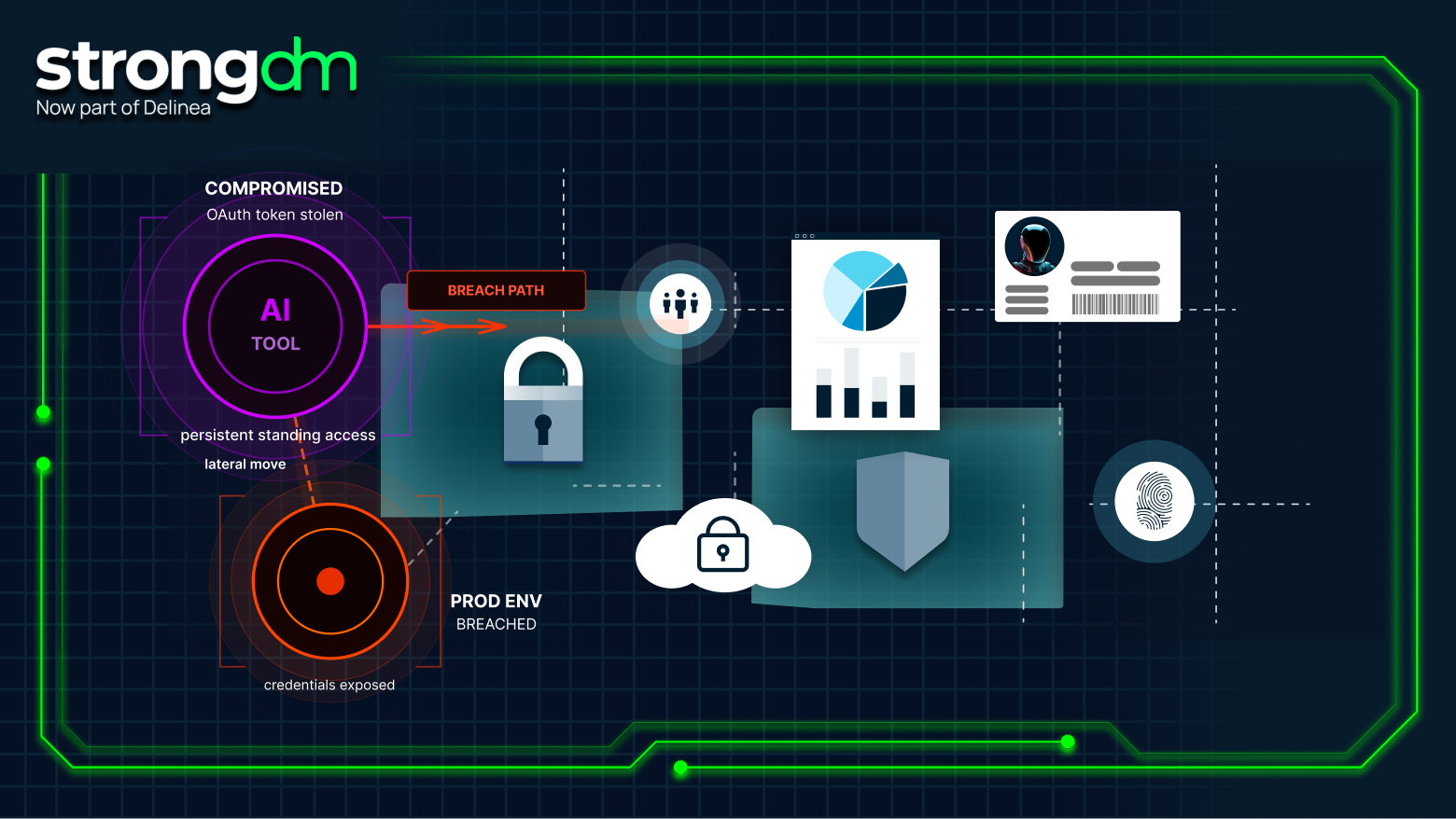
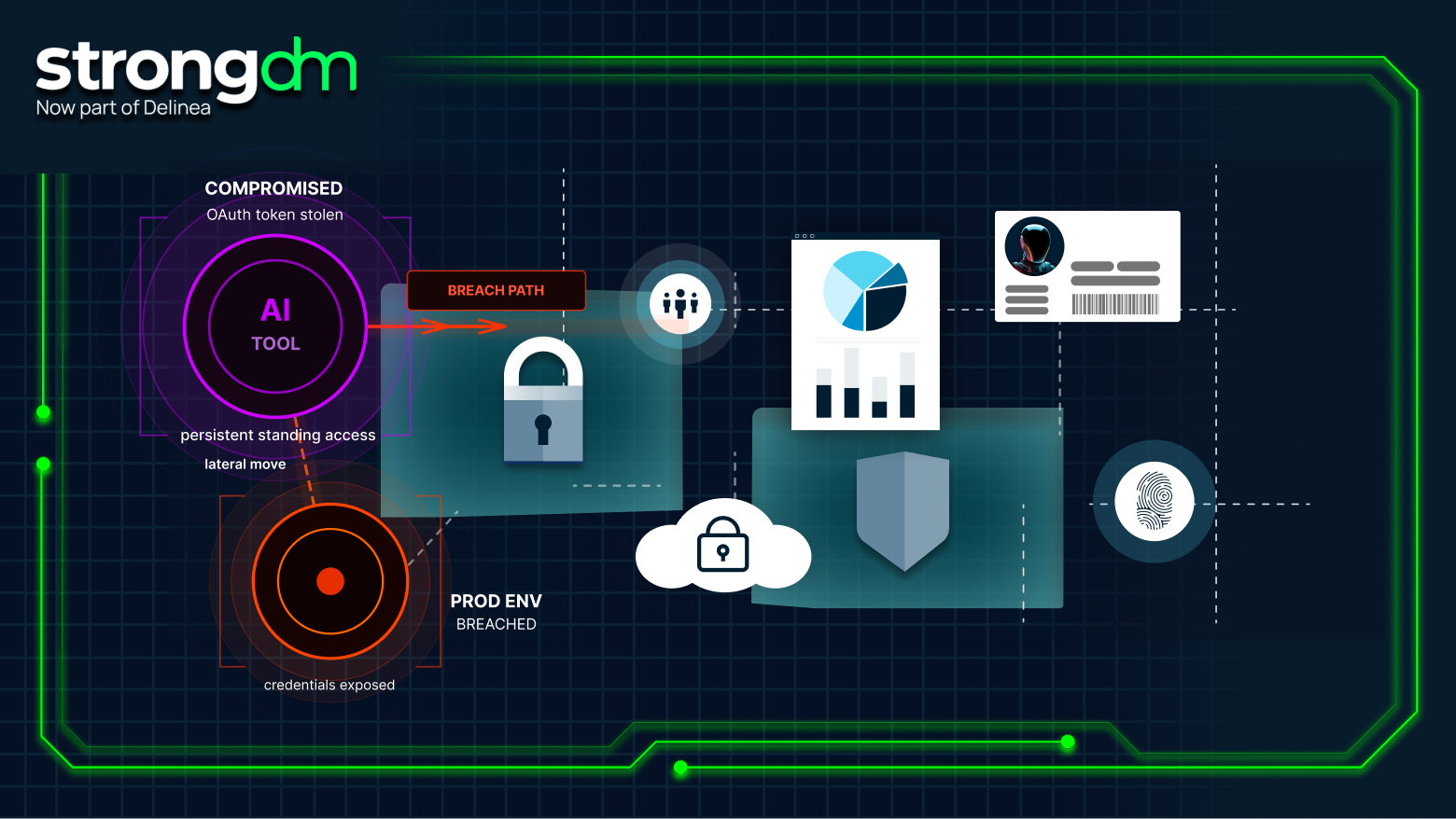
As AI agents take on actions once performed only by humans, traditional identity systems can’t provide clear delegation or accountability. StrongDM ID gives every agent a unique, verifiable identity linked to a human sponsor, ensuring organizations always know who authorized every action. In the next era of identity, authentication matters—but delegation defines trust.
DevSecOps means building secure software fast. But securing every layer of your stack, from code to containers to cloud infrastructure, takes more than patching vulnerabilities or running static scans. You need a coordinated toolkit.
This guide covers the core risks of hybrid cloud security, compliance, and operational, and the eight best practices for locking them down, from Zero Trust and JIT access to unified monitoring, segmentation, and incident response.
This guide lays out a clear framework for evaluating database security tools, focusing on the risks they mitigate, the controls they deliver, and the outcomes they enable. From access and auditing to encryption, posture management, and recovery, we’ll highlight the best solutions and how they fit together
This guide is your merger and acquisition security checklist, a 7-day playbook for securing privileged access during M&A. It’s built on lessons from enterprise CISOs, industry best practices, and what we see every day at StrongDM.

Data breaches are rising worldwide. Learn the latest stats, financial impact, and how to safeguard your organization with modern security.

Access certification is more than a checkbox; it’s how you prove and enforce least privilege at scale. It ensures every user, system, and role has only the access they need, nothing more. In this guide, you’ll learn how to run access certifications that satisfy auditors, reduce insider threats, and clean up outdated privileges. You’ll explore common types (manual vs. automated, user-based vs. resource-based), challenges, and how modern teams streamline the process with real-time visibility and
Authorization isn’t just about who gets in, it’s about what they can do once they’re inside. And that’s where most breaches happen. Whether you're enforcing RBAC, ABAC, or context-based policies, effective authorization ensures users only access what they need, no more, no less. This post unpacks how authorization works, compares key models, and explores best practices for enforcing least privilege at scale.

Workforce identity and access management (IAM) secures your internal users, employees, contractors, and engineers by verifying who they are, controlling what they can do, and monitoring how they interact with sensitive systems. It’s the foundation of Zero Trust in a cloud-first world. This guide breaks down everything from SSO and MFA to RBAC, JIT access, and directory services, and how they all work together to keep your workforce productive and protected.
Passwords alone don’t stop breaches anymore. Context-aware authentication changes the game by using real-time signals like device, location, time, and behavior to decide whether access should be granted.
StrongDM’s latest survey of 1,000 IT, compliance, and security professionals at financial institutions and fintech firms reveals a telling picture: while confidence in compliance planning is high, operational challenges persist, especially around privileged access management and audit preparedness.
Explore the top 7 secrets management tools, including StrongDM, HashiCorp Vault, AWS Secrets Manager, and Doppler. Discover secure, Zero Trust solutions that reduce secret sprawl, automate credential rotation, enforce least privilege, and integrate seamlessly with DevOps workflows.

Explore the best Kubernetes management tools, including StrongDM, Lens, Rancher, and Argo CD. Discover powerful solutions for cluster control, secure access, automation, observability, and cost optimization to streamline your Kubernetes infrastructure.
Single sign-on (SSO) gives users one login to access everything. SAML is one of the key protocols that makes that possible—passing identity data securely between identity providers and service providers. But while all SAML implementations are part of SSO, not all SSO solutions rely on SAML. Understanding how SAML fits into your authentication stack helps you choose the right tools for modern access control. This guide breaks down how SAML works, how it powers SSO, and how you can manage

