Simplify the offboarding process.
Just suspend a user in your identity provider and all access to backend resources is revoked automatically.
VPNs leave gaps in your security with their all-or-nothing design. They don’t enforce least privilege access that protects credentials. They don’t provide comprehensive audit trails. And they certainly don’t make for a positive end user experience.
Delegate authentication to your identity provider so you don’t have to manage separate systems.
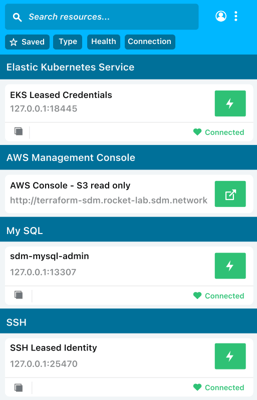
Authenticate to any database or server using your SSO. No need to distribute credentials, keys, or certificates to staff, reducing the risk of compromised credentials.

StrongDM has saved my team time by not having to create one-off users for each database and has allowed us to standardize the access control patterns. It has also been time-saving for ramping up new engineers who have the need to access all our data sources.”
StrongDM has saved my team time by not having to create one-off users for each database and has allowed us to standardize the access control patterns. It has also been time-saving for ramping up new engineers who have the need to access all our data sources.”


Just suspend a user in your identity provider and all access to backend resources is revoked automatically.
Anchored by the “never trust, always verify” principle to protect data, adopt a least privilege access model to avoid granting too much access to someone.
Grant access to only what’s required.
Monitor and manage every single device and user, whether inside or outside of the private network.