

Written by
Dominic GarciaLast updated on:
February 27, 2023Reading time:
Access Management: Are Those Workflows or Workarounds?
If you hope to embrace Modern Security this year, you’re not alone. As companies grow, innovate, and embrace new technologies, more employees need access to more critical systems. But with great access comes great responsibility.
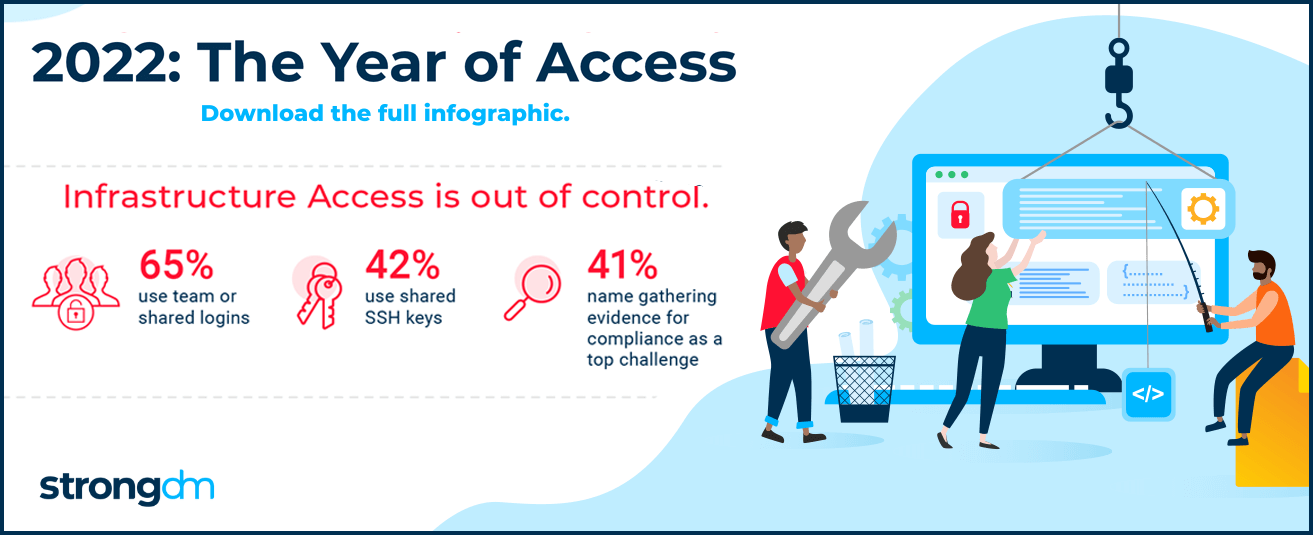
Existing workflows and processes that involve old-school methods don’t scale and are non-compliant. Access requests can take hours, days, or even weeks to fulfill. In our recent survey, 53% of organizations said they require hours to weeks just to get access to critical systems. It’s no wonder teams may try to ease friction by sharing logins and over-provisioning users, but these workarounds make organizations less secure and turn compliance documentation into a nightmare.
Access is foundational to not only enabling technical teams to do their jobs, but also to embracing modern security practices, such as Zero Trust. And when done well, it can improve your security posture while also delivering better efficiencies for your development and technical teams.
Zero Trust Is Aspirational, Access Is Addressable
In fact, in a recent podcast, Gartner analyst John Watts named access and identity as the critical starting points for adopting Zero Trust. Access to infrastructure has snowballed out of control, so it’s no surprise that as Zero Trust has gained steam, 80% of organizations are including access management as a critical initiative over the next 12 months.
One of the biggest issues is this challenge is additive. Access to every new technology or system must be managed in addition to all existing systems and technical debt. Traditional access control methods are unsustainable, and infrastructure access will only get more complex as organizations continue to embrace new technologies and the cloud, and as teams grow.
How do we know? In our survey, only 32% of teams listed Kubernetes as one of the most difficult technologies to manage in terms of access. This number is likely to increase as more organizations adopt this new and upcoming technology. In other words, the challenges inherent in managing access to ephemeral infrastructure have not been fully realized yet.
Access Management Is a Critical Initiative
Like DevOps, Zero Trust isn’t something you buy—it’s a methodology that you embrace. Access Management is an essential starting point for teams hoping to adopt modern security practices, such as Zero Trust, in 2022. When done well, it can improve your compliance posture, reduce overhead, and get your people connected to the systems they need when they need them.
Check out the full report, 2022: The Year of Access. Or if your organization is ready to embrace modern security, schedule a free demo of StrongDM to see how our infrastructure access platform can start you on the road to Zero Trust today.
Next Steps
StrongDM unifies access management across databases, servers, clusters, and more—for IT, security, and DevOps teams.
- Learn how StrongDM works
- Book a personalized demo
- Watch a StrongDM walkthrough


About the Author
Dominic Garcia, Technical Marketing Expert, has held marketing leadership roles for Silicon Valley technology companies specializing in database, data management, and data analytics solutions. As head of content marketing at Splunk, Dominic contributed to boosting the company’s market visibility and its growth from a $100M to a $1.3B company. He brings relentless creativity to the task of connecting people with technical products to improve their lives. Dominic holds a B.S. degree in Public Relations from the University of Texas at Austin. To contact Dominic, visit him on LinkedIn.
You May Also Like




