This blog is part one of a three-part series on Access Management 101. This series will walk you through how to get control of who has access, how to take inventory of all systems, and the cost of not taking these steps.
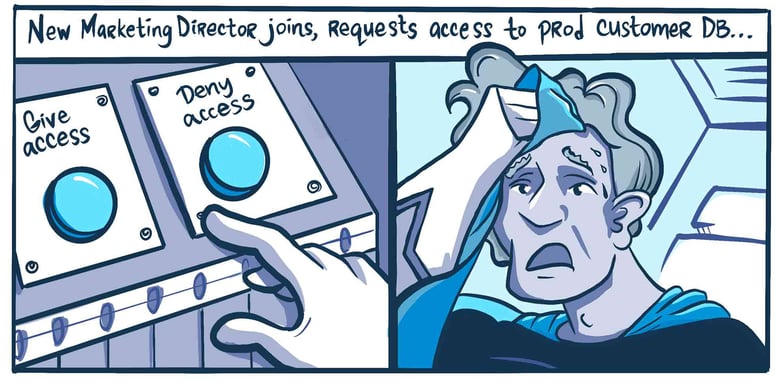
Here’s the scenario: On one side, you’re inundated with requests to provide access to critical infrastructure in order to enable teams to do their jobs; on the other side, you’re tasked with auditing access and ensuring that security to those systems is solid.
On top of that, you’re tasked with implementing some strategic initiatives, like ensuring all of your systems have embraced Zero Trust. And then you realize that you need to apply this across all of your servers, K8s, the cloud, databases...the list goes on. Where is that “bang head here” sign again?
The problem is easy to define; it’s just complexity. New technologies are released and used, employees or third-parties have come and gone, and there’s an unbelievable web that’s tying systems together.
The solution is easy to define too, but actually tackling it is extremely difficult, as it requires you to understand and document:
- Who has access.
- Whether those with access need it.
- When to provide/revoke access based on need.
- How to ensure that access is actively managed with an annual (or every few quarters) workflow.
Oh, and you need to do this across your entire company. Why? Because you can’t embrace Zero Trust if you’re not sure who is even in your infrastructure or what they’re doing there. Here you go: *Bang head here.* It’s time to take back control. And the best place to start is simply understanding the state of your infrastructure today.
What is Role & Access Discovery?
Access gets out of control for virtually every organization because most add employees, teams, roles, and systems over time, without a structured plan in place for how to do it. Organic growth in systems, new tools and technology, changes in teams and team structure, and a need to maintain legacy systems create challenges.
Without a process to track updates consistently, organizations inevitably reach the point where no one knows for certain which employees have or need access to which systems. This makes auditing a challenge, and employees get frustrated. Not to mention the headaches that come with tracking access given to third parties (contractors, vendors).
That’s where Role & Access Discovery comes in. Put simply, it’s a process to identify the internal roles of your organization and map out required infrastructure access for each role.
This isn’t a “what tool solves this?” problem because you’ll always be dealing with a level of organic growth (teams and systems). The goal is to implement a set of practices that will enable you to understand system access and maintain it over time.
In our experience, you need to begin with a human set of questions to foundationally understand the roles in your organization and the access required. This is going to take some time and cross-functional collaboration that will be critical to succeeding with this discovery process.
How to Standardize Roles & Access Across Your Organization
The good news is that it’s possible to drive an initiative that standardizes roles and access across your organization. The granularity with which you define roles and access is important, so you’ll need to collaborate across IT, DevOps, HR, and Security teams to decide how to categorize roles and manage access for each one.
Here are some considerations & best practices:
- Partner across your organization to understand roles and required access, including across HR and IT.
- Create a process to review the list on a quarterly or bi-quarterly basis, which means you need to keep it up to date.
- Standardize how you deliver access, taking an automated and secure approach where possible.
The critical piece here is to develop the relationships and processes required to audit access across people and systems on a consistent basis. Consistency is key. Although simply mapping it out is helpful, every organization is organic, with new tools being acquired, and people coming and going. And once you get started, managing access will be greatly simplified in the future.
How to Get Started with Role & Access Management
Stay tuned for part two of this series, which will document how to take back control on the systems side. In the meantime, here are a few tools to help you get started.
- Download our interactive Role & Access Discovery Workbook.
- Prefer a walkthrough? Watch our on-demand webinar.
- Take a look at our Getting Started checklist.
Next Steps
StrongDM unifies access management across databases, servers, clusters, and more—for IT, security, and DevOps teams.
- Learn how StrongDM works
- Book a personalized demo
- Watch a StrongDM walkthrough


About the Author
Justin McCarthy, Co-founder / CTO, originally developed empathy for Operations as a founding and pager-carrying member of many operations and data teams. As an Executive, he has led Engineering and Product in high-throughput and high-stakes e-Commerce, financial, and AI products. Justin is the original author of StrongDM's core protocol-aware proxy technology. To contact Justin, visit him on Twitter.
You May Also Like